Ledger is one of the most famous manufacturers of hardware wallets for storing cryptocurrency. The company has always confidently boasted of the security of its devices, but in early 2018 a vulnerability was...
Ledger is one of the most famous manufacturers of hardware wallets for storing cryptocurrency. The company has always confidently boasted of the security of its devices, but in early 2018 a vulnerability was found in the Ledger Nano S wallet. The company closed the security hole in the new firmware version 1.4.1, which was automatically updated on all devices.
But it turns out that wallets are still vulnerable in the case of physical access of the attacker. British schoolboy, Salim Rashid, described in detail and demonstrated an attack on the Ledger Nano S and Ledger Blue devices in his blog.
Due to the fact that the cryptographic chips of the devices do not support displays and USB, the communication functions are assigned to an additional microcontroller called an MCU.
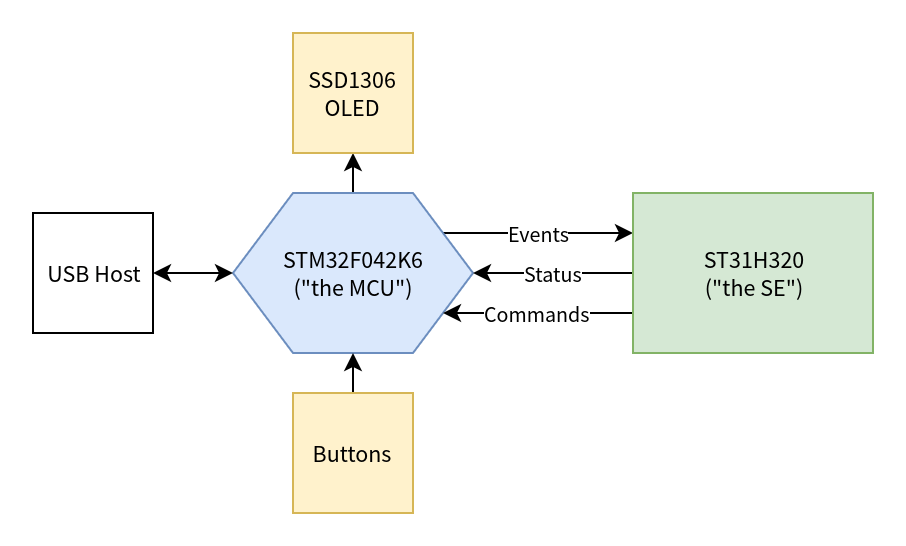
Salim Rashid wrote a script that makes the MCU present an original version of the firmware to the cryptographic module, although in fact the wallet is compromised.
Rashid wrote to the developers about the problem as early as November 2017. The company responded that the security system does not imply physical access to the wallet by the hacker. It is interesting that in 2015 Ledger said that it is impossible to modify or replace the firmware without a private key, which means that you can safely buy wallets of the company on Amazon or eBay.
The method of breaking into the devices, demonstrated by Rashid, does not depend on the firmware version since it is designed for an auxiliary module. An investigation of the 15 year old Briton's method was evaluated by professional security specialists. They confirmed that modern Ledger wallets are susceptible to hacking and also noted the elegance of the method that Rashid offered.
In early 2018, Ledger raised $75 million for additional research and expansion of the company.
Share this with your friends!





Be the first to comment
Please log in to comment