The malware is based on the Ryuk cypher, but instead of demanding ransom, it simply steals files.
The MalwareHunterTeam has discovered a new virus based on Ryuk ransomware, but unlike the original malware it does not demand ransom from the victim or encrypt the files.
After entering the victim’s computer, the virus scans the system directories in search of .docx and .xlsx files. The program compares the contents of the files with a special directory. Judging by the words in this directory, the program’s creators are interested in secret documents created by military and financial organizations, as well as materials related to criminal cases. Some of the keywords included ‘breach’, ‘tank’, ‘defence’, ‘military’, ‘verification’, ‘secret’, ‘confidential’, ‘undercover’, ‘federal’ and others.
It’s interesting to note that the virus also searches for names, including ‘Emma’, ‘Liam’, ‘Olivia’, ‘Noah’, ‘William’, ‘Isabella’, ‘James’, ‘Sophia’ and ‘Logan’.
The dissemination patterns of the virus have not been identified yet. Potentially interesting files are loaded to the FTP server 66.42.76.46/files_server/a8-5.
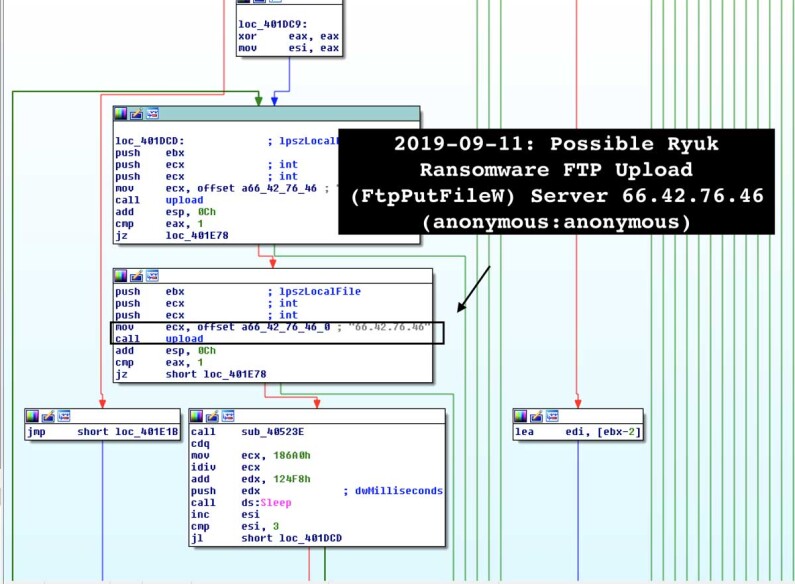
Due to similarities to Ryuk ransomware, it’s likely that either the creators of Ryuk modified its code to search for confidential documents, or someone got access to the source code of the cypher.
Share this with your friends!



Be the first to comment
Please log in to comment